Table of Contents
Being a talent acquisition leader isn’t just about understanding people. Today, you have to balance between being a people expert, a shrewd budget manager, and when it comes to new tech, a guardian of data security. With a growing pile of hats to wear, the one that requires deep tech-savviness can feel particularly oversized.
You’re tasked with protecting sensitive data, but without a computer science degree, how do you sift through the jargon to ensure your vendor’s security promises hold water? Every vendor is going to promise you “enterprise-grade security,” but what does that actually mean?
I teamed up with Jen Vesp, a CISSP-certified Information Security Analyst at GoodTime, who brings 15 years of experience in data security to help you understand exactly what matters when it comes to your data. Below, we decode the technical talk, help you identify the security essentials, and empower you with key questions that cut through the marketing speak (trust me — as a marketer myself, I can spot it a mile away). At GoodTime, we’ve never failed a security risk assessment from a single customer or prospect — including some of the strictest enterprise organizations like Sony Interactive Entertainment, Slack, and Lyft — so we like to think we have a thing or two to share about what good data security looks like.
By the end of this article, you’ll not only understand what to demand from your HR technology vendor regarding data security and privacy but also be equipped to hold them accountable. It’s about making sure that “enterprise-grade security” is not just a buzzword, but something you can truly understand and rely on.
Here are 11 things you should ask every HR tech provider you’re considering.
1. How comprehensive is your data encryption, both at rest and in transit?
When we talk about data encryption, we’re referring to the conversion of data into a code to prevent unauthorized access. Imagine it as turning your data into a secret language that only those with the ‘key’ can understand. Now, there are two places where this data needs this protective cloak: at rest (when it’s stored) and in transit (when it’s moving from one place to another, like from your device to the cloud).
Why is this important? Think of it as fortifying your castle. Encrypting data at rest ensures that even if invaders breach the walls (hackers getting through your defenses), they can’t interpret the treasures they find. Encrypting data in transit is like safeguarding it on a dangerous journey across the kingdom, deterring bandits who might intercept it.
What to look for: Ask for specifics — what type of encryption do they use? Is it the industry-standard AES 256-bit encryption, or something else? Also, verify that encryption doesn’t stop at your perimeter but extends to every corner of their service.
Where GoodTime stands: GoodTime’s security program leverages top-tier encryption protocols to secure data at all stages, making sure your data is as secure in transit as it is at rest. This ensures comprehensive protection that meets and exceeds industry standards, keeping your sensitive information under a veil of security that rivals that of the most secure digital fortresses.
2. Can your system guarantee compliance with global data privacy regulations?
In the digital age, data knows no borders. This interconnectedness demands compliance with a patchwork of global data privacy regulations, regardless of where your company is headquartered. Whether it’s the GDPR in Europe, CCPA in California, or other regional laws, these frameworks are the guardians of personal data rights and corporate data handling practices.
Why is this important? Global operations mean global responsibilities. With candidates and employees spread across continents, your HR tech vendor must navigate the intricate web of international data privacy laws. It’s a matter not just of legal necessity but of building trust with a globally distributed workforce. Compliance assures that your operations respect personal data no matter where your employees log in from.
What to look for: Seek an HR tech vendor that doesn’t just claim to be compliant, but who can demonstrate a proactive and thorough approach to global data regulations. They should provide a clear map of their compliance landscape, complete with certifications and regular audit reports that reinforce their commitment to global data stewardship.
Where GoodTime stands: Recognizing the global stage on which modern enterprises operate, GoodTime has crafted a platform that adheres to the stringent standards set by international data protection laws. We proudly uphold compliance with SOC 2 Type II, GDPR, CCPA, HIPAA/HITECH Type 1, and more — ensuring that your company’s use of our platform aligns with the highest principles of data privacy worldwide.
3. What is your protocol for security breaches and how quickly do you respond?
A security breach protocol is akin to a fire drill — it’s crucial to have a plan in place before an emergency strikes. In the digital realm, this plan outlines the steps a company will take in the event of unauthorized access to data. It’s not just about having shields; it’s about having a skilled response team ready at a moment’s notice.
Why is this important? Breaches can happen to even the most fortified systems. When they do, speed and precision in response are critical. The right protocol can mean the difference between a contained incident and a full-blown data disaster. It’s about being ready to act swiftly to minimize damage and restore security.
What to look for: Inquire about their incident response time, which is how quickly they can spring into action following a breach. Do they have dedicated personnel for such emergencies? How do they communicate with their clients during a crisis? And importantly, ask for a history of their response to past incidents.
Where GoodTime stands: At GoodTime, we implement a rapid response protocol for any breach, ensuring that reaction times are swift and effective. Our dedicated security team is prepared to leap into action, with communication lines always open to provide transparency and updates to our clients. We commit to not just meeting but exceeding industry response standards, ensuring that your trust in our system is well-placed and upheld, even in the face of the unexpected. We’re happy to report that to date, we haven’t had any security incidents or breaches, but we’re ready to respond swiftly should one occur.
4. How do you handle data ownership and transfer if we choose to switch providers in the future?
Data ownership and the ability to transfer it securely when switching providers is like having the freedom to move to a new home with all your belongings. It’s essential to know that you can pack up your data and take it with you without complications, should you decide to change providers in the future.
Why is this important? Your data is one of your most valuable assets. Ensuring that you retain ownership and control over it even when ending a relationship with a vendor is critical. It prevents lock-in and ensures business continuity. The ease with which you can transfer data to a new system can impact operational efficiency and safeguard against data loss.
What to look for: The vendor should provide clear terms on data ownership in their service agreement. Ask about the process for data extraction and the formats provided. You should look for assurances that your data can be returned or destroyed upon request.
Where GoodTime stands: Our commitment to data portability is ironclad. With GoodTime, you retain ownership of your data, with the added benefit that data retention periods are defined by you, the customer. We also provide straightforward procedures for data extraction, ensuring our customers receive their data in usable formats, and facilitating a smooth transition, should they ever choose to migrate to another provider.
5. Do you have full-time, certified in-house team members dedicated to security?
Ensuring strong data security is not just about having the right tools and protocols; it’s also about having the right people in place. Dedicated, certified security professionals play a pivotal role in maintaining and enhancing an organization’s security posture.
Why is this important? Cybersecurity threats are dynamic and ever-evolving, requiring constant vigilance and specialized knowledge to counteract. Full-time, certified security professionals are equipped with the latest insights and practices needed to protect sensitive data effectively. Their presence indicates an organization’s commitment to security at the highest level.
What to look for: Ask potential HR tech vendors if they employ full-time security personnel with recognized certifications, such as CISSP (Certified Information Systems Security Professional). These certifications are indicators of a deep, formalized understanding of security principles and practices.
Where GoodTime stands: At GoodTime, we don’t just prioritize top-notch security technologies; we also invest in top-tier talent. We have a full-time, CISSP-certified Information Security Analyst on staff, alongside engineers who are deeply committed to integrating the strongest data security measures into all our development efforts. This dual focus on both human and technological resources ensures that our security strategies are robust, proactive, and up to the task of protecting your most valuable assets.
6. What level of security training do your employees undergo?
A tech provider’s employees are often the first line of defense against potential security threats, which makes their training crucial for maintaining the integrity of the entire system.
Why is this important? Security is only as strong as its weakest link. Employees who are well-trained in security best practices can identify and mitigate risks before they become breaches. Conversely, untrained employees may inadvertently become entry points for security threats.
What to look for: Ask potential vendors about the type and frequency of security training their employees undergo. This should include training on recognizing phishing attempts, securing personal devices, and understanding the importance of maintaining strict access controls. The best training programs are continuous, adapting to the evolving landscape of cyber threats.
Where GoodTime stands: We ensure that all employees undergo comprehensive security training as part of their onboarding process, with ongoing training sessions conducted regularly. This includes ongoing tests to ensure knowledge retention and readiness. Our proactive approach to security education helps maintain a vigilant and informed team, dedicated to safeguarding your data.
7. Do you provide disaster recovery solutions and how do they protect against data loss?
Disaster recovery solutions are like emergency backup generators — they kick in when things go awry, ensuring that operations can continue with minimal disruption. These solutions involve strategies and technologies that help restore data and systems after a disaster, such as a cyber attack, natural disaster, or human error.
Why is this important? In today’s digital world, the resilience of your business operations hinges on the ability to quickly recover from disruptions. Effective disaster recovery plans minimize downtime and data loss, which are critical for maintaining operational continuity and protecting against potentially catastrophic losses.
What to look for: Inquire about the vendor’s disaster recovery capabilities and their data recovery time objectives (RTOs) and data recovery point objectives (RPOs). These metrics will tell you how quickly they can restore operations after an incident and how much data might be lost in the process, respectively.
Where GoodTime stands: GoodTime is equipped with a robust disaster recovery plan that includes geographically distributed data centers to ensure redundancy. Our RTOs and RPOs are designed to guarantee that operations can be rapidly restored with minimal data loss, providing peace of mind that your critical data is always protected, even in the face of unforeseen disruptions.
8. Can your platform offer data hosting options that align with our company’s geographic location and compliance needs?
You can think of choosing your data hosting location like choosing the right environment for a safe deposit box — it needs to be secure, accessible, and in a location that aligns with your legal and operational requirements. This is particularly relevant for companies operating across different international jurisdictions, where data residency requirements might dictate where data must be physically stored.
Why is this important? Different countries have varying regulations about where and how data should be stored and handled. Compliance with these regulations not only protects you legally but also builds trust with your customers and employees by showing that you respect their local laws and preferences.
What to look for: Ensure that the vendor can offer data hosting options that comply with the specific legal requirements of the countries in which you operate. This includes having the capability to store data in specific regions and offering choices about data transfer and storage.
Where GoodTime stands: GoodTime provides flexible data hosting solutions designed to meet the specific needs of our global clients. We offer our customers full control over their data — including the option to have their data stored and processed on servers in the European Union, ensuring compliance with the highest standards of European data privacy regulations.
9. How transparent is your platform in reporting data security metrics and incident reports?
Transparency in reporting data security metrics and incident reports is like having a clear, unobstructed view of the health of your home’s security system. It’s essential to understand how well your data is protected and identify any potential vulnerabilities that need addressing.
Why is this important? Regular updates and clear communication about security posture and incidents help you stay informed about how your data is being handled and protected. These updates build trust and ensure that both you and the vendor are actively engaged in safeguarding the information.
What to look for: Ask if the vendor provides regular security audits, compliance reports, real-time system status, and timely alerts about security incidents. The detail and frequency of these reports can greatly impact your ability to respond quickly to security issues.
Where GoodTime stands: We believe in complete transparency with our clients. We provide detailed security reports and notifications about any incidents within 72 hours, backed by comprehensive audits and compliance checks. Our approach ensures that you are always informed and prepared, reinforcing our commitment to maintaining the highest standards of data security.
10. What third-party security certifications and audits does your platform hold?
Third-party security certifications and audits act like endorsements from respected authorities that verify a vendor’s security practices are up to standard. These certifications are important because they provide an independent assessment of the security measures a company has in place.
Why is this important? Just as a stamp of approval from a regulatory body can instill confidence in a product, security certifications reassure you that the vendor’s security infrastructure has been rigorously tested and meets specific industry standards. This helps mitigate risks and ensures that the vendor is committed to maintaining high levels of security.
What to look for: Look for widely recognized security certifications such as ISO 27001, SOC 2 Type II, and PCI DSS. These certifications indicate that the vendor has met stringent security requirements set by third-party organizations. Also look out for companies touting outdated or invalidated certifications such as Privacy Shield, which could signal that their entire data security operation hasn’t been updated or assessed recently.
Where GoodTime stands: GoodTime holds multiple top-tier security certifications, including SOC 2 Type II, GDPR, and CCPA compliance. We are also among a very small number of HR tech providers that hold the HIPAA/HITECH Type 1 certifications that are crucial for healthcare organizations. Our systems undergo regular third-party audits to verify that our security practices are not only current but also aligned with the best industry standards. This commitment to certified security demonstrates our dedication to protecting your data with the utmost rigor.
11. How do you secure the API and integration points with other systems?
No software exists in a vacuum. Any platform you’re evaluating likely relies on integrations and APIs so it can interface with your current systems and create a seamless experience for your users. Integration points are where your system interacts with other services (like your calendaring, email, and video conferencing systems), and they can be vulnerable to attacks if not properly secured.
Why is this important? As businesses increasingly rely on a diverse ecosystem of applications and services, the interfaces (APIs) that connect these systems become critical junctions that must be protected. A breach at any integration point can compromise the entire network, making robust security measures essential.
What to look for: Inquire about the security measures in place for API and system integrations. This includes authentication protocols, encryption of data in transit, and regular security testing of the integration points. Ensure that the vendor adheres to best practices for API security such as using OAuth for authentication, HTTPS for secure communication, and providing detailed logging and monitoring.
Where GoodTime stands: GoodTime’s integrations employ stringent security protocols. We use state-of-the-art authentication mechanisms, including OAuth and secure token-based authentication, to ensure that only authorized entities have access. All data transferred through our APIs is encrypted using HTTPS, and we conduct regular security assessments to identify and mitigate potential vulnerabilities. This comprehensive approach ensures that our integration points remain fortified against unauthorized access, safeguarding the seamless and secure operation of your interconnected systems.
Now you’re ready to cut through the security noise
Navigating the complexities of HR tech security might seem daunting, but armed with the right questions, you’re now equipped to cut through the veneer of technical jargon and truly assess what matters. Remember, every vendor will tout “enterprise-grade security,” but your newfound insights will help you challenge these claims and demand evidence that stands up to scrutiny.
As you move forward, consider these questions not just as a checklist but as part of an ongoing dialogue with your HR tech providers. It’s about building partnerships with vendors who not only promise but also prove that they can safeguard your data with as much care as you invest in your people.
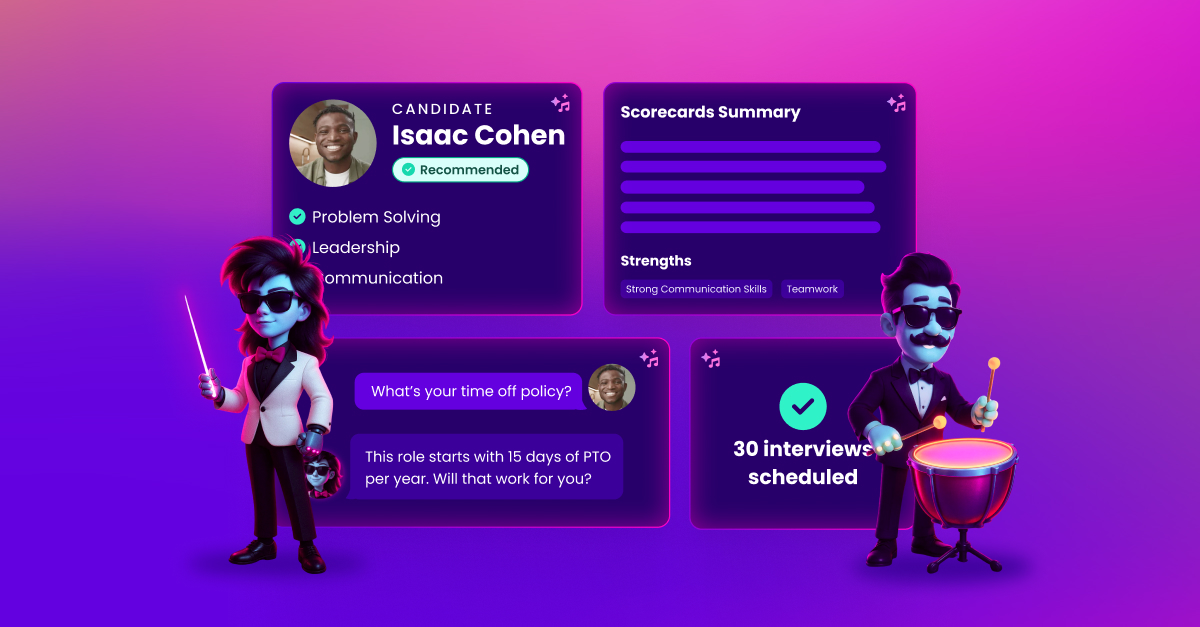
GoodTime is committed to being more than just a vendor; we aim to be a trusted partner in your entire talent acquisition journey. Our 100% security risk assessment approval rate is driven by our transparent practices, rigorous security measures, and commitment to compliance. We’re all about ensuring that “enterprise-grade security” is more than a buzzword — it’s your reality. So, as you don the hat of a data security guardian, take comfort in knowing that with GoodTime, you have a partner that’s equipped to support you every step of the way.
All the benefits of human-centric AI, no compromises on security
Automate 90% of interview management tasks, elevate your hiring experiences, and never compromise on data security.